Cloud or On-site Storage?
Companies have begun removing their data from cloud storage solutions in a trend called cloud repatriation, moving their cloud-based workloads to on-site infrastructures like enterprise data centers, colocation providers, and managed service providers. Let’s talk...
What is Blockchain?
The term “blockchain” describes an advanced digital database mechanism that stores data in blocks. These blocks are linked together as a chain, as the name suggests. In layman’s terms, a blockchain is a set of data stored in the cloud. The databases are meant to be...
Co-Managed vs Managed IT Services
Having IT support for your business is a no-brainer. IT services are essential for a successful business. But there are a lot of decisions that go into choosing which IT service is right for you. One of the most important is whether or not to choose co-managed IT...
The Security of AI and Large Language Models
It’s no secret that artificial intelligence (AI) is on the rise. People and businesses are using it to write their copy, craft their designs, and even strategize their businesses. But when you remove the human barrier from work, it poses a security risk. Who or what...
The Safety and Security of Business Messaging Platforms
It’s almost a guarantee that we all use some type of messaging platform or app in our day-to-day lives at work. Slack, Teams, Google, and the list goes on. But have you ever stopped to think about the security of these platforms (or lack thereof)? Or about what...
What is Malware?
Simply put, malware is malicious software—”any program or file that is intentionally harmful to a computer, network, or server.” Cyber criminals can implant malware onto your devices or into your network through cloud access or even emailing a file. It can be...
Why You Need a Password Manager
We’re sorry to be the bearers of bad news, but your “luckykitty92” password from middle school is a lot easier to crack than you’d like to believe. But, we also know that long and strong passwords are difficult to remember. Enter: password managers! These tools help...
What is Data Exfiltration?
As a business, the data you keep safe is probably your most important asset and possession, aside from your clients or customers. So what happens when cyber criminals get ahold of that data? Or if an employee leaves the company and takes any sensitive data they have...
Everything You Need to Know About Cookies
Unfortunately, cookies are not just a sweet treat to enjoy with milk. They also exist in technology! We’re sure you’ve seen a little pop up on websites that says something along the lines of: “This website uses cookies” with accept, decline, and manage buttons. Most...
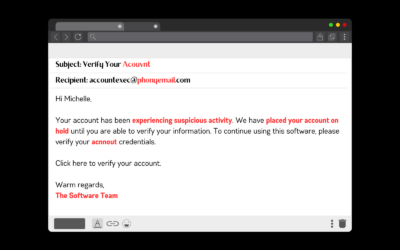
How to Spot and Avoid Phishing Scams
Phishing—not fishing—is a common cybersecurity scam. It’s relatively easy to fall prey to these scams, and they can be hard to detect. So it’s important to know what phishing scams are, common things to look out for, and how to protect yourself from them. Let’s get...