Just because your network has spam filtering on doesn’t mean your business is safe from phishing attacks. Even with the right tools protecting your system, knowing the signs of phishing emails remains among the most effective ways to neutralize their threat.
Phishing is one of the greatest threats to businesses today. Besides tricking employees into giving away their login credentials, phishing emails also spread ransomware, viruses, and other cyberthreats.
In phishing, hackers owe much of their success to social engineering tactics, which are methods used to fool your staff into believing he or she is reading a legitimate message. Understanding these tactics will help potential victims identify suspicious emails and protect themselves from data breaches and infections by malware.
What are the signs of a phishing email?
Hackers will go to great lengths to make a phishing email appear as believable as possible. If a phishing attack specifically targets your company, for instance, hackers may research the names of your managers, clients, or vendors. They will then use these names to make their email appear trustworthy.
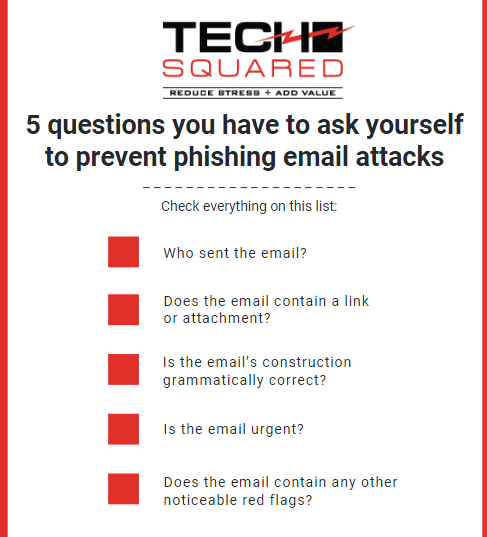
Therefore, even when an email appears to come from someone within your organization, always ask these questions:
#1. Who sent the email?
Hackers understand that most employees are unlikely to ignore an email from their boss. This is why phishing emails are usually made to look like they came from a CEO, department head, or manager in your company. Hackers may also use the name of a customer, investor, or vendor.
With that in mind, check if the email is actually sent from the sender’s email address on your records. A common tactic used by hackers is to take a legitimate domain or email platform and replace one of its letters with characters that look similar. For instance, instead of “[email protected]” the address says “[email protected]”.
#2. Does the email contain a link or attachment?
Phishing emails won’t harm your computer or network unless you click on the link or attachment they contain. The URL could appear as though it comes from reliable sources, albeit with tiny variations, such as a misspelling or characters in upper case. When you hover your mouse pointer over the link, you may also notice that the link-to address is different from its URL. Clicking on the link may take you to a malicious website or trigger a download.
Similarly, the attachments in phishing emails may appear like legitimate documents, such as greeting cards and forms. Oftentimes, they appear unrelated to the rest of the email’s contents or message and are in potentially dangerous file types, such as .exe, .doc, and .pdf. Downloading and opening them infects your system with malware, so it’s best to leave them as is.
#3. Is the email’s construction grammatically correct?
Executives, clients, and even your colleagues understand just how crucial a business email can be, so they’d usually pay attention to elements like grammar and spelling. On the other hand, hackers aren’t always conscious of these factors. If you find that the email contains more than the reasonable number of grammatical and spelling errors, then it’s best to assume it’s phishing or spam.
#4. Is the email urgent?
Another tactic hackers use is to make their email seem urgent. They usually do this by sounding irate or making it seem as if any delay would incur a penalty for your company. The message may also threaten to sue the receiver or expose compromising pictures, videos, or information. This puts the recipient on edge and more likely to follow directions.
The best course of action is to stay calm. If you can, verify the sender’s identity. You may also verify the request by inquiring directly through the sender’s contact details you have on record.
#5. Does the email contain any other noticeable red flags?
You may also look for these other suspicious signals:
- The email contains words the sender doesn’t normally use or point to information the user wouldn’t normally know.
- You’re CC’d in the email, but you do not know the other people the message was sent to.
- The email’s subject is unrelated to its content.
Tech Squared has years of experience protecting companies in Virginia from phishing and other types of cyberthreats. To start boosting your business’s security, learn what solutions you need by downloading this eBook today!
More Than Just Tech Support